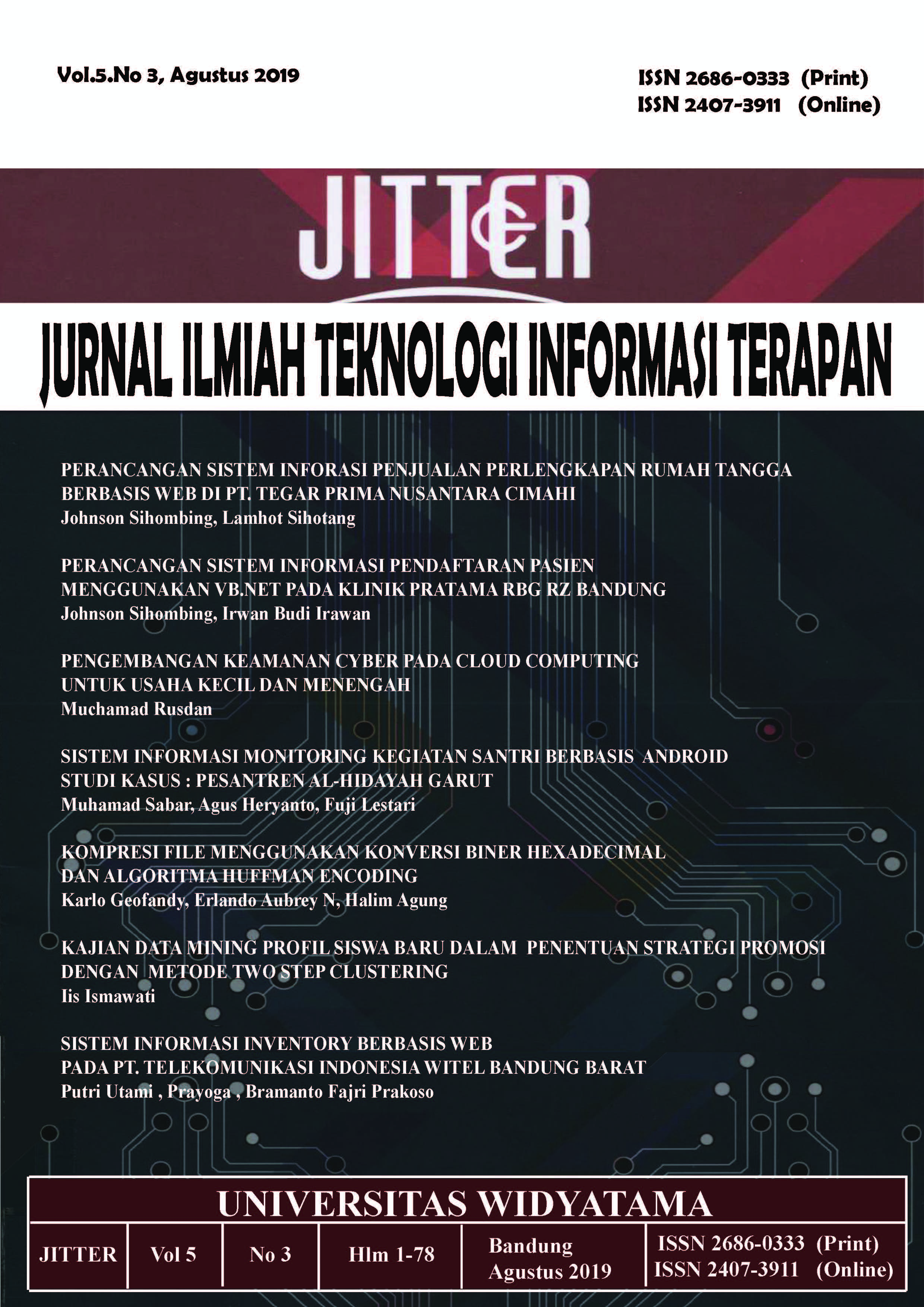
PENGEMBANGAN KEAMANAN CYBER PADA CLOUD COMPUTING UNTUK USAHA KECIL DAN MENENGAH
DOI:
https://doi.org/10.33197/jitter.vol5.iss3.2019.298Keywords:
Cyber Security, SME, Cloud ComputingAbstract
The main objective of this research is to test effective security strategies for SMEs on cloud computing technology, by examining security threats for SMEs, mitigation measures, and the best strategies for effective security in a cloud computing environment. Cloud computing is a relatively new paradigm that presents significant business benefits and enormous opportunities for small and medium businesses. As the information technology (IT) landscape develops, SMEs need to find effective strategies to meet business demands. However, many SMEs are reluctant to adopt cloud computing technology due to inherent security, privacy, and trust issues, as well as regulatory risks and compliance implications. Preliminary studies show an increasing number of cybersecurity attacks targeting SMEs in the cloud environment. To address security threats, there is a need to establish best practices, standards, and guidelines that can be followed by SMEs. This study addresses two research objectives: (i) to identify security threats and challenges facing SMEs in the cloud environment and determine the best mitigation strategies and, (ii) to develop a security strategy framework for SMEs in the context of cloud computing. The overall contribution of this research is the proposed model, which integrates four strategic components: the Cloud Model, the Security Model, the Compliance Model, and the Main Security Component.
Downloads
Downloads
Published
How to Cite
Issue
Section
License
Submission of a manuscript implies that the submitted work has not been published before (except as part of a thesis or report, or abstract); that it is not under consideration for publication elsewhere; that its publication has been approved by all co-authors. If and when the manuscript is accepted for publication, the author(s) still hold the copyright and retain publishing rights without restrictions. Authors or others are allowed to multiply the article as long as not for commercial purposes. For the new invention, authors are suggested to manage its patent before published. The license type is CC-BY-SA 4.0.